Having and Implementing Best Practice Guidance - Course Monster Blog Generic
Why is it important to own a book that contains qualified, best practice guidance?
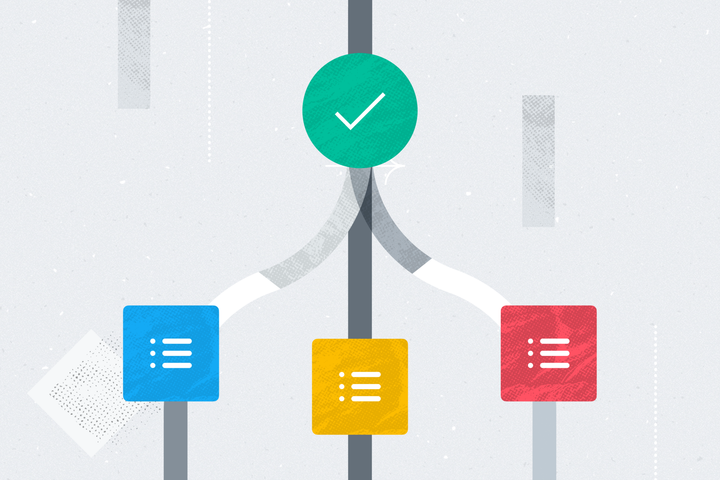
Managing projects before the existence of project management systems such as PRINCE2 was like being lost in a forest without a map. In addition to not understanding where to go next, project managers tended to make