PAT Scopes are now Supported by all Azure DevOps REST APIs - Course Monster Blog

The Azure DevOps team recently implemented a change to connect all of their REST APIs with a specific personal access token ( PAT ) scopes as part of their efforts to improve security. Before this change, some of these APIs were not tied to a PAT scopes, which could potentially lead to customers using full-scoped PATs to access them. Full-scoped PATs grant access to all the permissions of the corresponding user and could be misused by malicious actors to access sensitive information such as source code or production infrastructure. By associating these APIs with a PAT scope, the Azure DevOps team is reducing the risks associated with a compromised PAT credential.
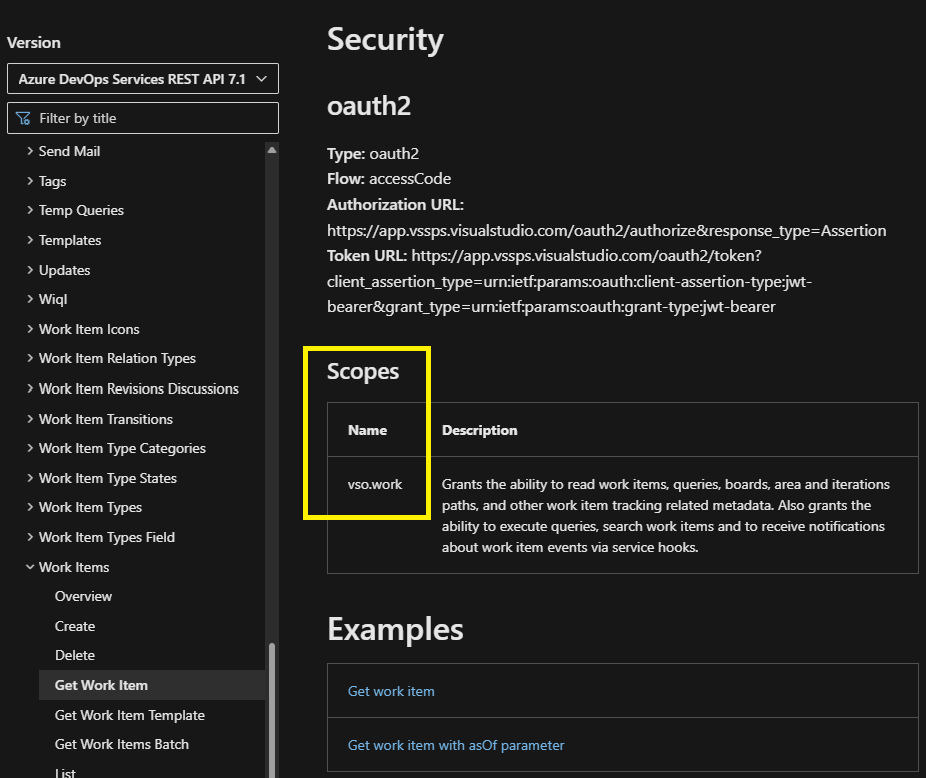
If you are using a full-scoped personal access token (PAT) to authenticate to an Azure DevOps REST API, you should consider switching to a PAT with a more specific scope to limit access. The specific scopes accepted by each API are listed in the “Security” section of the API’s documentation. By using a PAT with the appropriate scope, you can avoid granting unnecessary access.
Additionally, these improvements should allow more customers to prevent the creation of full-scoped personal access tokens (PATs) by enabling the corresponding control plane policy.
Want to know more about Microsoft Azure? Visit our course now.
Here at CourseMonster, we know how hard it may be to find the right time and funds for training. We provide effective training programs that enable you to select the training option that best meets the demands of your company.
For more information, please get in touch with one of our course advisers today or contact us at training@coursemonster.com



Comments ()